What Is Blockchain Technology?
A blockchain technology is a distributed database that is shared among the nodes of a computer network or in other words, a blockchain is essentially a digital ledger of transactions and tracking assets that is duplicated and distributed across the entire network of computer systems. An asset can be tangible like a house, car, land, cash, jewels or intangible like intellectual property, NFT, branding, patents or content copyrights.
Every time a new transaction occurs on the blockchain technology, a record of that transaction is added to every participant’s ledger. The decentralised database managed by multiple participants is known as Distributed Ledger Technology (DLT).
Blockchain technology are popular because of its crucial role in cryptocurrency systems, such as Bitcoin, Ethereum, Bitcoin Cash, Dogecoin, Tron and Litecoin, are secured via blockchain networks.
Why Blockchain Technology Is Popular ?
Suppose you are transferring money to your friend from your bank account. You simply would login to your bank portal website and transfer the amount to your friend using their account number.
When the transaction is completed, your bank updates the transaction records in their database. But these types of transactions can be tampered with very quickly. Keeping record of the data and transactions in database is a crucial part of the business. In most cases database information is handled in house or passed through a third party like brokers or bankers increasing time as well as cost.
Most normal databases, such as an SQL database, have someone in charge who can change the entries in database. Blockchain is different because nobody is in charge; it’s run by the people who use it and it avoids the long process and facilitates the faster movement of the transaction, thereby saving both time and money.
Key Elements of Blockchain Technology
1. Distributed Ledger Technology (DLT)
In blockchain technology all network participants have access to the distributed ledger. Distributed Ledger Technology (DLT) is a protocol that enables the secure functioning of a decentralized digital database. It allows for storage of all information in a secure and accurate manner using cryptography.
2. Immutable Records
Immutability is defined as the ability of a blockchain ledger to remain unchanged, unaltered, and indelible. Means no participant can change or tamper with a transaction after it’s been recorded to the shared ledger.
3. Smart Contracts
It is a set of rules — is stored on the blockchain. These digital contracts are executed automatically once rules/conditions are met. Smart contract facilitate, verify, or negotiate a contract agreement of a transactions.
How Does Blockchain Technology Work?
The main objective of blockchain technology is to allow digital information to be recorded and distributed among the computer nodes, but not edited and centralized. Records of transactions that cannot be tempered, deleted, or destroyed. This is why blockchains are known as a distributed ledger technology (DLT).
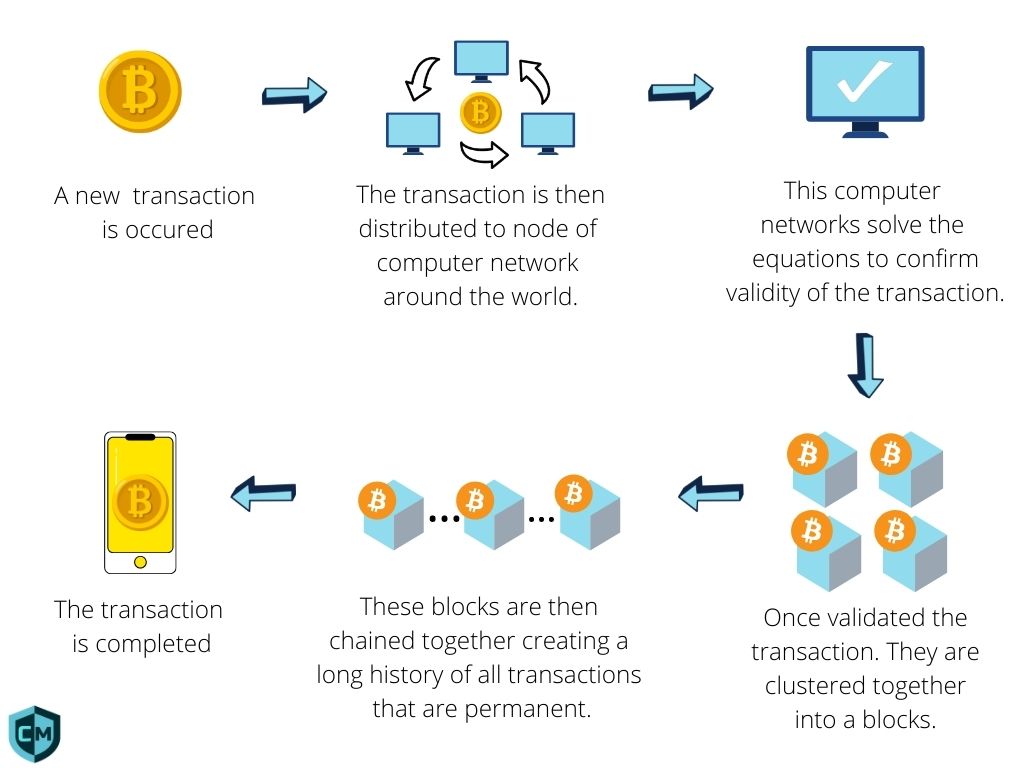
- When a new transaction is occured, here transaction show the movement of an asset that can be tangible (a product) or intangible (intellectual) is distributed to the nodes of computer network across the world.
- These computer networks utilize their processing power to solve the equations and validate the transaction between buyer and seller.
- After validating the transaction, it is recorded as a “block” of data.
- These blocks form a chain of data as an asset moves from place to place. The blocks confirm the exact time and sequence of transactions, and the blocks link securely together to prevent any block from being altered or a block being inserted between two existing blocks. Each additional block strengthens the verification of the previous block and hence the entire blockchain.
- As a result, the transaction is completed with security.
Usecase of Blockchain Technology
Crypto Currencies
Most cryptocurrencies use blockchain technology to record transactions. For example, the Bitcoin, Litecoin and Ethereum are based on blockchain. Cryptocurrencies are digital currencies (or tokens) that can be used to buy goods and services. Just like a digital form of cash.
Normal currencies are controlled by the Government or Bank, If a bank is hacked, the client’s private information is at risk. But crypto currencies are difficult to hack.
Healthcare
Healthcare providers can use blockchain technology to securely store their patients’ health records. When a medical record is generated and signed, it can be written into the blockchain, which provides patients with the proof and confidence that the record cannot be altered.
Smart Contracts
Another blockchain innovation is self-executing contracts commonly called “smart contracts also known as digital contracts”. Smart contracts operate under a set of conditions to which users agree. These digital contracts are executed automatically once rules/conditions are met. Smart contract facilitate, verify, or negotiate a contract agreement of a transactions. For instance, a payment for a good might be released instantly once the buyer and seller have met all specified parameters for a deal.
Non-Fungible Tokens (NFTs)
Ethereum programmers can create tokens to represent any kind of digital asset, track its ownership. NFTs are unique blockchain based tokens that store digital media (like an image, video, music or art). Each NFT has the ability to verify authenticity, past history and sole ownership of the piece of digital assets. NFTs have become piece of mouth in these days because they offer digital creators the ability to buy and sell their creations, while getting proper credit and a share of profits.
Web 3.0
Web 3.0 (or simply web3) is the third generation of the Internet that interconnects data in a decentralized way to deliver a secure, faster and more personalized experience to the user.
Technologies like machine learning (ML), artificial intelligence (AI), Big Data, semantic web, decentralized ledger technology (DLT) etc. are used to build the web 3.0 internet. To keep data safe and secure web 3.0 uses blockchain technology.
Advantages of Blockchain Technology
Data Transparency: Due to use of blockchain technology, user will track their data and inspect the code behind the platform.
Uninterrupted Service: In blockchain data is stored on multiple nodes to ensure redundancy. So there is no single point of failure due to information stored on multiple locations.
Data Privacy: The most significant advantage of blockchain technology is data encryption to protect the user information from disclosure.
Data/content Ownership: With the help of Non-Fungible Tokens (NFTs) users will gain complete ownership and control of their information.
No Need for Intermediaries: Transaction can confirm and complete without working through a third party. This saves time as well as the cost of paying for an intermediary like a bank.
Disadvantages of Blockchain Technology
Potential for Illegal Activity: Due to decentralization in blockchain is difficult to regulate. This might lead to an increase in cybercrime and online abuse.
Blockchain use cryptography which involve public and private keys. If user loses their private key, they face numerous challenges, making this one disadvantage of blockchains.
Requires advanced computer devices: Blockchain can save users money on transaction fees but the technology is far from free. For example bitcoin transaction required a large amount of computational power.
Scalability Restrictions: Blockchain depends on a larger network to approve transactions. The number of transactions per node is limited. For example, Bitcoin can only process 4.6 transactions per second.
FAQ
1 What is an Information Security?
Information Security sometimes called InfoSec, act of protecting data & information from unauthorized access, unlawful modification & disruption, disclosure & destruction. Read more
2 What is WEB 3.0 ?
Web 3.0 is the third generation of the Internet that interconnects data in a decentralized way to deliver a secure, faster and more personalized experience to the user. Read more
3 What is Malware?
Malware is malicious software or program designed to infiltrate a computer system/network and possible damage it without the user’s knowledge or consent. Read more
4 What is Cyber Kill Chain?
The cyber kill chain is a way to understand the sequence of events involved in an external attack on an organization’s IT environment Read more
5 What is Public Key Cryptography?
Asymmetric Cryptography also popular as public key cryptography, uses two keys to encrypt data. One key is used for data encryption, while the other key is used for data decryption. Read more
6 Difference between Stream & Block Cipher?
Stream Cipher & Block Cipher, both are the techniques used for encryption and decryption of data, i.e. to convert the plaintext to cipher text and cipher text to plaintext. Read more